These questions probably wouldn't have entered your thoughts when you are setting up your password and each one of those occasions when you have disregarded the reminder about changing your password after a specific time.
Just to hold you knowledgeable about how protected your password is from the modern-day world right here are some fascinating statistics As of your studying this, greater than 8.2 million passwords are stolen every single day. This has led to over 16.7 million humans in the United States having their records stolen. This value them greater than 16.8 billion dollars, greater than $1,000 per person.
The purpose of these statistics to have these large numbers reported is now not simply due to the fact the password you have saved is vulnerable however its simply now not the excellent way to defend your account or identity.
That is what we are right here for today, to talk about how we can make this a little bit extra tougher for someone in the pc world.
What is the additional step we are going to discuss?
Its new two-step verification features allow you to add an extra layer of security that that can ensure your online accounts– including your email, social media, internet shopping, and individual money accounts to be protected.

The fundamental notion in the back of this method is to double Test that your identification is legitimate.
Different names it has been given by various organizations such as Two-factor authentication, also called multiple-factor or multiple-step verification
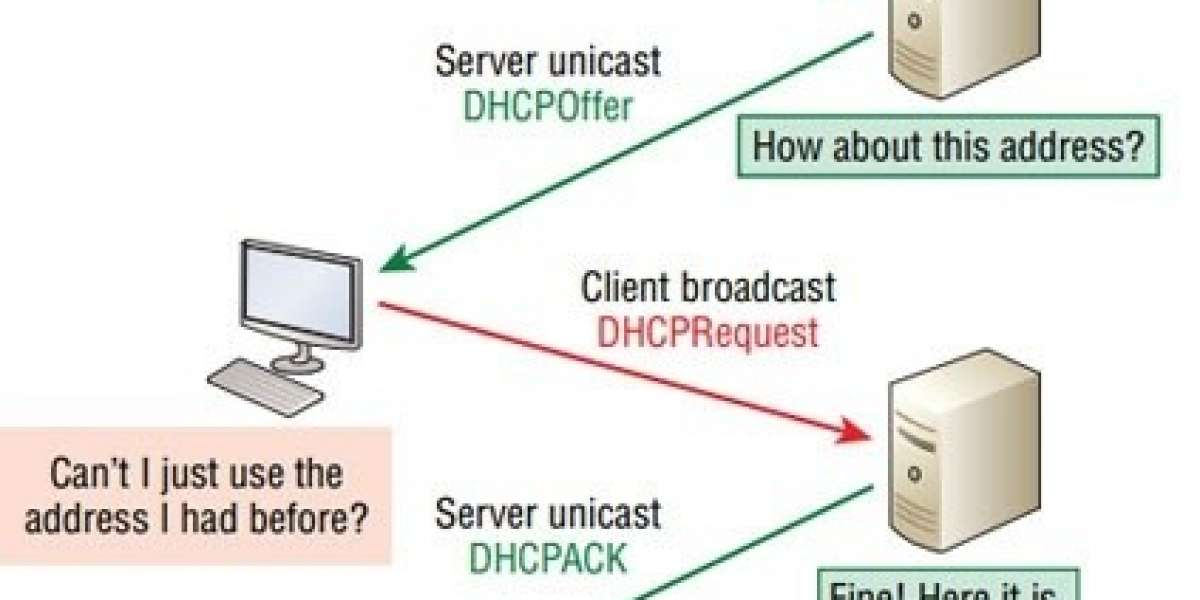
Simply put, two-factor authentication provides a 2nd step in your regular log-in process. Once you enter your username and password, you will be prompted to enter a code dispatched as a textual content message or an email, or on occasion as a push notification on your phone.
It uses the combinations of your password with something you have (i.e. a mobile) or something which you are (i.e. facial recognition or fingerprint authorization)
Why You Should Use Two-Factor Authentication?
As I clarified toward the start of this feature, two-factor authentication helps protect your sensitive, personal data by verifying your identification.
Take applications or sites such as Dropbox, Google, or iCloud, for instance. On any of these administrations, you will store a great deal of individual data and images, and on iCloud or Google, you may synchronize your contacts, schedules, and email, and everything which is put away on the phone is likewise backed up on the cloud concerning your email ID.
Simply envision the measure of data a person would have about you on the off chance that they had the option to get through your password and get hold of your information.

Sure, two-factor authentication is a bit of an annoyance, at least the first time you log in on a device. Set up another iPhone, for instance, and it will take you some time to get every one of your records going. (You need to do this for each new gadget, since every gadget sends its exceptional identifier to a login server, and validation is required when you sign in on another gadget.)
The burden of this is far exceeded by the additional security you get when utilizing two-factor confirmation.
Another strong reason to consider 2FA is shown in the image below provided by Google which shares the data that the 2-factor authentication blocks 100% of automated bot

Receiving a secondary SMS code blocked 100% of automated attacks, 96% of bulk phishing attacks, and 76% of direct, centered attacks – like these made using employed hackers. Using on-device prompts brings these numbers up to 100, 99, and 90%, respectively. The enhancement is in all likelihood due to the truth that it’s more difficult to get anyone to tap an on-Receiving a secondary SMS code blocked 100% of automated attacks, 96% of bulk phishing attacks, and 76% of direct, centered attacks – like these made through employed hackers. Using on-device prompts brings these numbers up to 100, 99, and 90%, respectively. The enhancement is likely due to the truth that it is more difficult to get any one to tap an on-device instant than it is to strive to dupe them into giving away an access code. Of course, the use of a physical protection key is safest, blockading a hundred percentage of every type of attack throughout Google ‘s report. Device instant than it is to strive to dupe them into giving away an access code. Of course, the use of a physical protection key is safest, blockading a hundred percentage of every type of attack throughout Google‘s report.
Kinds of Two Factor Authorization
Generally, multi-factor authentication systems rely on at least one of the following approaches:
- Authenticator Apps: Authenticator apps are exactly what they sound like: smartphone apps that handle the second-factor approval process as standard notifications. Authenticator apps such as Duo Mobile use internet connectivity to deliver login approval requests, which is more secure than using phone lines.
- U2F devices: Universal Second-Factor (U2F) devices are similar to tokens: they’re small physical devices used exclusively to verify logins. Instead of attaching to a keychain like a token, however, U2F devices are designed to fit in an open USB slot. (Older models use USB-A ports, newer versions fit in USB-C slots.) When a user enters their password on a computer with a U2F device plugged in, they’re prompted to tap the physical U2F device to gain access. U2F devices are popular because they’re so easy to use — a simple tap and you’re done — but using one means giving up an available USB port, which isn’t always an option for all users.
- Passcodes. Passcodes are the most common form of 2FA, and usually consist of a short string of numbers sent to a smartphone. Passcodes count as 2FA. Since they rely on phone lines, however — which can be compromised — they represent the least secure method. Passcodes aren’t a real hit with users, either: each code must be manually entered, which can be a nuisance.
- Tokens: Many web security teams opt to arm their users with tokens. These typically are small keychain fobs that generate codes for users to enter as their second factor. Tokens are more secure than cellular-delivered passcodes, as they don’t rely on phone lines, but they don’t address the annoyance of entering codes. (In fact, they may make that worse, as you can’t copy and paste a code from a token.) Tokens are attractive because they are affordable and don’t require system administrators to collect phone numbers — but they’re battery-operated, and batteries die. Using tokens will mean dealing with the headache of timing replacements to avoid users losing access to crucial systems.
- Phone callbacks: Phone callbacks are one of the less popular versions of 2FA, but they’re an effective — if time-consuming — way to implement a second factor. In a phone callback setup, once a user logs in, they receive an automated phone call that prompts them to approve or deny the access request.
- TOTP: Time-based One-Time Passcodes, better known as TOTP, are similar to passcodes. Instead of a service sending the user a series of numbers, however, an app generates a one-time-use passcode that will quickly expire. Doing it this way means users can still use their authenticator app (which will generate TOTPs on demand), and no insecure phone lines get involved.
What to Do If Two Factor Authentication isn't Offered
Two-factor authentication has been around for a while, however, it’s nonetheless one of the most beneficial extra layers of safety you can get. All of Google’s accounts have a 2FA functionality that can be utilized using your phone, and equipment token, or the Google Authenticator application. So on the off chance that you were worrying about not having two-factor validation choices, you're secured.
However, not every platform or service offers two-factor authentication. Are you simply out of luck in protecting accounts that don’t have it?
Google’s solution—have these systems use Google’s open-source code to build their two-factor authentication software. At first, this seems like a convenient solution to get companies to use another of Google’s products to solve a common problem. However, Google is doing anybody a favor by offering such a predominant safety technique that these agencies should have already have implemented.
So if you’re searching to disable two-step verification on Gmail, Apple, Yahoo!, or any different service, think about what you’re about to do. two-step authentication may additionally now not be perfect, however, it’s higher than solely relying on your password to defend your account. While it does now not clear up all the issues of today’s hacker-filled world, we consider that two-factor authentication is moving us in the proper course towards whole online protection.
Two-factor verification is an absolute necessity have for:
- online banking
- online shopping (Amazon, PayPal – however it's just accessible for a couple of nations)
- email (Gmail, Yahoo, Outlook)
- cloud capacity accounts (Dropbox, Box, Sync)
- accounts on informal communities (Facebook, Twitter, Linkedin, Tumblr)
- productivity applications (Evernote, Trello)
- password directors (LastPass)
- communication applications (Slack, Skype, MailChimp)
Conclusion
Having a password and an extra factor authentication does now not make your account one hundred percent secure. It’s now not a magic wand, that will make your account unhackable. No, it solely makes it extra hard to breach.
Ideally, an assailant will proceed onward to another objective, one that is less secure, instead of investing a ton of time in vitality attempting to penetrate your second-validation factor.
But, as two-factor authentication strategies will come to be greater popular, new approaches for attackers to crack them will additionally pop out. It’s simply how the security game is played.
You have to swap on 2FA at any place possible. As they say, prevention is better than cure. It’s important to never rely on any single method for comprehensive protection. That means two things: (1) if you’re presently relying on passwords alone, it’s time to evolve, and using 2FA is a solid first step; and (2) 2FA is an essential security tool, but it becomes even more effective when it’s used as part of a coordinated strategy of security applications and policies.